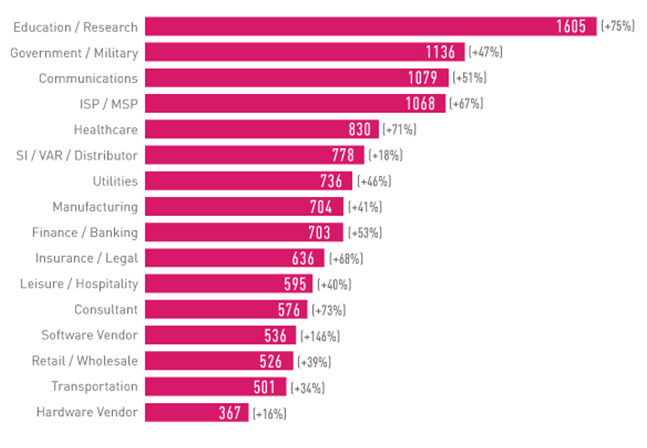
Overall in 2021, organizations experienced 50% more weekly cyber-attacks than in 2020. With the Education/Research sector’s 1,605 weekly attacks taking the lead (75% increase). This was followed by Government/Military with 1,136 weekly attacks (47% increase) and Communications with 1,079 weekly attacks (51% increase). These are the findings of the “Cyber Attack Trends: 2022 Security Report” released by Check Point Research (CPR).
Software vendors experienced the largest year-on-year growth (146%) which goes hand-in-hand with the ever-increasing trend of software supply chain attacks observed in 2021. This last year has also seen evolving attacks on mobile devices, increase in major cloud services vulnerabilities, and the return of the notorious Emotet botnet.
Highlights from the “Cyber Attack Trends: 2022 Security Report” are
- Supply chain attacks: the infamous SolarWinds attack laid the foundations for a supply chain attack frenzy. 2021 saw numerous sophisticated attacks such as Codecov in April and Kaseya in July, concluding with the Log4j vulnerability that was exposed in December. The striking impact achieved by this one vulnerability in an open-source library demonstrates the immense inherent risk in software supply chains.
- Cyber-attacks disrupting everyday life: 2021 saw a large number of attacks targeting critical infrastructure which led to huge disruption to individuals’ day-to-day lives, and in some cases even threatened their sense of physical security.
- Cloud services under attack: Cloud provider vulnerabilities became much more alarming in 2021 than they were previously. The vulnerabilities exposed throughout the year have allowed attackers, for varying timeframes, to execute arbitrary code, escalate to root privileges, access mass amounts of private content, and even cross between different environments.
- Developments in the mobile landscape: Throughout the year, threat actors have increasingly used smishing (SMS phishing) for malware distribution and have invested substantial efforts in hacking social media accounts to obtain access to mobile devices. The continued digitization of the banking sector in 2021 led to the introduction of various apps designed to limit face-to-face interactions, and those, in turn, have led to the distribution of new threats.
- Cracks in the ransomware ecosystem: Governments and law enforcement agencies changed their stance on organized ransomware groups in 2021, turning from preemptive and reactive measures to proactive offensive operations against the ransomware operators, their funds, and supporting infrastructure. The major shift happened following the Colonial Pipeline incident in May which made the Biden administration realize they had to step up efforts to combat this threat.
- Return of Emotet: One of the most dangerous and infamous botnets in history, is back. Since Emotet’s November return, CPR found the malware’s activity to be at least 50% of the level seen in January 2021, shortly before its initial takedown. This rising trend continued throughout December with several end-of-year campaigns and is expected to continue well into 2022, at least until the next takedown attempt.
The findings of the “Cyber Attack Trends: 2022 Security Report” are based on drawn from Check Point Software’s ThreatCloud Intelligence between January and December 2021, highlighting the key tactics cyber-criminals are using to attack businesses.